Surge in ransomware attacks threatens student data
University student details has develop into more and more threatened as cyberattacks on faculties intensify this year.
This tactic of details exfiltration and extortion, which has develop into specially common in ransomware assaults, puts added force on faculties to spend hefty ransoms in get to shield the privateness of its students. On best of demands triggered by the frenzied swap to distant finding out, faculties will have to adapt to new threats like these every single working day.
For illustration, the Clark County Faculty District (CCSD) in Nevada was strike by a ransomware attack on Aug. 27, which might have resulted in the leak of pupil details. When it came time to make the conclusion no matter whether to spend, the college procedure declined. The district posted an update on Sept. 28 stating it was knowledgeable of media reviews claiming pupil details experienced been exposed on the net as retribution for not paying out the ransom.
“CCSD is performing diligently to establish the whole mother nature and scope of the incident and is cooperating with legislation enforcement. The District is not able to confirm numerous of the promises in the media reviews,” the update study.
On Sept. thirty, the district posted a Detect of Data Privateness Incident on its’ web-site, which mentions the probability of leaked details.
“Whilst CCSD’s investigation is ongoing and has been not able to establish no matter whether any specific file containing delicate info was basically accessed or acquired by the unauthorized actor, CCSD’s investigation established that particular current and previous staff info might have been accessed or acquired by the unauthorized actor. As a result, in an abundance of caution, CCSD is notifying folks, such as particular current and previous workforce, of this incident whose identify and Social Security numbers ended up current in the affected devices at the time of the incident.”
Brett Callow, risk analyst at antimalware vendor Emsisoft, stated the CCSD details was posted on the Maze ransomware group’s leak website, which exists on equally the crystal clear and darkish webs [Maze’s web-site was offline at press time]. Maze pioneered the tactic of extorting victims through threatening to leak private details. In addition to CCSD, Callow stated you will find been a major uptick in the quantity of thriving assaults on college districts in modern weeks.
“At the very least 12 districts have been strike this month by yourself, with the assaults interrupting training at up to 595 faculties. Data was stolen and published in 5 of these 12 conditions,” he stated.
One particular month following the ransomware incident impacted CCSD, reviews of one more risk commenced rolling in: phishing cellphone calls. The district took to Fb to tackle problems.
“The Clark County Faculty District (CCSD) has gained reviews of some folks receiving phishing cellphone calls by numbers that look to be related to CCSD. These calls are not currently being designed by CCSD faculties and look to be a 3rd-celebration spoofing caller ID and utilizing robocalls to endeavor to phish and demand payment. Remember to know that CCSD would not demand payment by cellphone. CCSD is knowledgeable of the make any difference and is investigating. If you acquire these types of a cellphone call, please disregard it.”
It really is unclear if the phishing calls are related to final month’s ransomware attack. SearchSecurity arrived at out to CCSD for comment but have not heard back again.
The risk of details publicity might force victims to spend ransoms. But Invoice Conner, CEO of protection vendor SonicWall, stated when it comes to deciding no matter whether to give into the blackmail, the moment you spend, you’ll be on the list endlessly, “They’re going to just hold coming back again to that college. And the moment they strike a single, they are going to go to the upcoming a single.”
The moment the risk of stolen details results in being an concern, Conner thinks of it more as identification theft.
“You can choose age, gender and obtain that. The moment you steal that details, it results in being precious on the darkish internet on numerous various characteristics,” he stated. “Even if you do spend, you will find a 50{d11068cee6a5c14bc1230e191cd2ec553067ecb641ed9b4e647acef6cc316fdd} likelihood you might not be in a position to get better your details in any case. Even if they get the details back again, it would not indicate you will find not a duplicate someplace in the wild.”
Common targets
Risk actors have lengthy qualified K-12 faculties and better training in the past, but these types of assaults have raise amid the change to distant finding out through the COVID-19 pandemic. “They are exceptionally vulnerable even more than they ended up a single year ago,” Conner stated.
New research by endpoint protection vendor Absolute Program examined the consequences of distance finding out on endpoint overall health, system usage, safety and protection as faculties adapt to distant and hybrid finding out styles in the 2020-2021 college year. It established that 60{d11068cee6a5c14bc1230e191cd2ec553067ecb641ed9b4e647acef6cc316fdd} of all malware assaults, specially ransomware, occur in training.
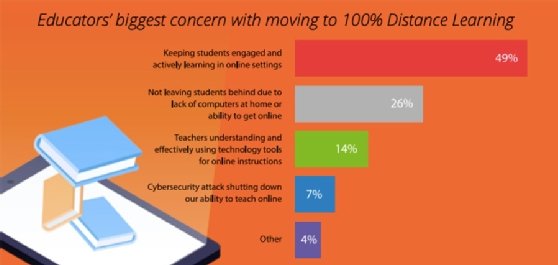
Endpoint safety vendor Morphisec also unveiled new study, which examined COVID-19’s affect on the new, virtual college year and consisted of in excess of 500 instructors and directors throughout the U.S. who ended up surveyed in July. In accordance to the report, “irrespective of ransomware assaults increasing in quantity and sophistication, in excess of half of K-12 educators say their institution has not warned them about the specific potential risks of ransomware. In simple fact, throughout equally K-12 and better ed establishments, just 13{d11068cee6a5c14bc1230e191cd2ec553067ecb641ed9b4e647acef6cc316fdd} of educators say they really feel ransomware poses the most major risk as they shift to distance finding out environments.”
As evident from the Nevada Faculty District ransomware attack, Fairfax County General public Educational institutions and many others, ransomware is posing a single of the largest threats. Since COVID-19 introduced on a need to swap to distant finding out so swiftly, faculties did not have substantially time to change, generating them all the more vulnerable.
Andrew Homer, vice president of protection strategy at Morphisec, stated schools’ boards are putting large force on educators to figure out distance finding out and protection simultaneously, although teaching.
“Distance finding out just massively opened up a massive attack floor due to the fact now you are utilizing unhardened collaboration apps like Zoom and at the very same time, these machines are now distant so how are you heading to update them, patch them?” he stated. “These are all unexpected issues. They are currently being pressured to do more with less and these young ones in K-12 are the less accountable individuals around protection cleanliness. It really is the perfect storm kind situation.”
Consciousness around the expanded attack floor is one more worry and is not perfectly comprehended by the instructors, faculty and personnel who are basically deploying the distance finding out remedies, Homer stated.
In accordance to the study by Absolute, “distant finding out is generating tech assist challenges that are using away precious time for instructors to “instruct.” The details confirmed 9 out of ten instructors claimed shelling out more time troubleshooting technological innovation complications.
“They’re are not knowledge what the threats are that tends to make them vulnerable. Enabling these collaboration apps, acquiring these machines exterior the college procedure and the implications around that, it is really no shock that numerous have by now been attacked,” he stated. “We know Zoom is currently being qualified. These are apps that have not witnessed widescale usage. What is worrisome is you will find no raise in shelling out or finances or personnel to fight this looming risk.”
Morphisec carried out a demonstration where by risk researchers broke into Zoom and ended up in a position to use it as an info stealer to scrape qualifications and basically record classes unbeknownst to end users. “They are simple to crack due to the fact they haven’t been utilized in company and mission-essential kind environments up until finally now. And you can go correct down the line no matter whether it is really Slack or Webex,” Homer stated.
In accordance to Absolute details, there was a 141{d11068cee6a5c14bc1230e191cd2ec553067ecb641ed9b4e647acef6cc316fdd} raise in collaboration software package, such as BlueJeans, Skype, Microsoft Teams and numerous well known equipment.
One particular explanation K-12 is an simple focus on is the weak protection posture, Conner stated. Remote finding out is only amplifying the potential risks. “Educational institutions are not constantly the very best at cybersecurity or backing up. And now, it is really exceptionally dispersed networks.”
Conner also stated numerous challenges going through the new college year merely occur down to a lack of cash for K-12 college devices.
“A very best practice would be to truly start to phase the networks. Place various apps and identities in various degrees of protection. If you are an admin or affiliated with financials, you need to be in a substantially more protected system, not just at the college but at your residence,” Conner stated.
Absolute details suggests that forty six{d11068cee6a5c14bc1230e191cd2ec553067ecb641ed9b4e647acef6cc316fdd} of faculties have at the very least a single system that works by using rogue or nonauthorized VPN or internet proxy apps, “but it only normally takes a single vulnerable system to generate a protection incident.”
The hurry to get distant finding out up and working also resulted in sick-preparedness, Homer stated. “Everybody from the superintendent to the board of trustees are deeply involved about ransomware, they just you should not have a good plan on how to protect against it and protect against some of these assaults due to the fact they have been so centered on enabling distance finding out,” he stated.
Attackers identify these flaws, generating faculties an even a lot easier focus on.
“They have their company model, too. They can go following K-12, which they know are not patching their devices, they’re vulnerable to utilizing these collaboration apps and go following them. It really is substantially a lot easier with recognised exploits than they can with an company enterprise that has a robust, layered defense in depth strategy.”







