Druva integrates with FireEye Helix for secure backups
Druva has solid an API integration with FireEye Helix to present IT security groups who is accessing and doing backup tasks.
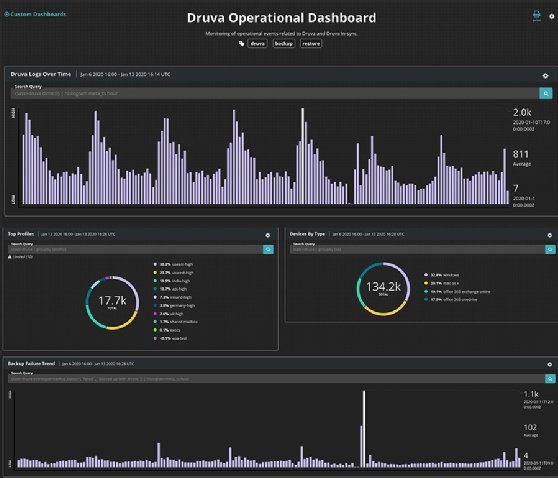
Joint buyers using Druva InSync for endpoint and cloud software backup and FireEye Helix for security can use the integration to fight ransomware attacks. By extending FireEye’s visibility into Druva, the suppliers let security admins to observe backup and restore activities by means of Helix’s interface. Preset procedures and alerts aid establish when something is amiss, these as abnormal details restoration, unauthorized login attempts, password improvements and admin attempts to obtain details. This enables admins to react to opportunity details breaches or theft, no matter if from a ransomware assault or an insider.
Naveen Chhabra, senior analyst at Forrester Research, claimed bridging the gap in between security and details defense needs to materialize at the technologies degree and the administrative degree to maintain corporations secure from fashionable threats. A single of the challenges of recovering from a ransomware assault is determining which backup level to restore to. Some ransomware is insidious plenty of to lie dormant following intrusion and wait for backups to replicate it, compromising all foreseeable future copies. With right monitoring, IT security would be ready to establish the level of intrusion and recommend process admins to restore backups from right before then. Having said that, Chhabra claimed quite often, security and backup admins are not chatting to each and every other plenty of.
And even if they have been, scale gets a challenge. Chhabra claimed technologies has to stage in with applications that can get better hundreds or countless numbers of compromised VMs in an automatic, structured fashion. Information and facts in between backup and security applications need to have to be shared intelligently in get to establish a workflow of determining which VMs need to have to be restored and which copies are “cleanse” and secure to restore from.
“The obstacle now is restoration at scale. Hunting at this holistically is normally welcome,” Chhabra claimed.
Prem Ananthakrishnan, vice president of merchandise at Druva, claimed ransomware attacks on backups have greater since the COVID-19 pandemic. More people functioning remotely supplies higher options for criminals to steal credentials or gain unauthorized entry to backups. Apart from cybercriminals trying to get out an organization’s final line of protection, Ananthakrishnan claimed insider threats have also greater. A slow financial system and the worry of layoffs can push personnel to go rogue, primary to details theft or destructive deletion.
“From the volume of assist cases we get, we are viewing an increasing craze wherever buyers suspect people have been trying to split into their backup process,” Ananthakrishnan claimed.
“Threats are shifting to at-household staff,” extra Sean Morton, vice president of buyer knowledge at FireEye.
Morton claimed from a security standpoint, the coronavirus and the ensuing greater distant function was currently increasing the assault area for cyber intrusion. Having said that, following three months or more of mandated isolation and slowed company, morale across several organizations has diminished. Businesses are now dealing with a higher risk of details leakage from within than right before.
Ananthakrishnan claimed security admins have normally struggled with speedily obtaining incident info when it will come to backup. Druva is a backup item and would as a result be below the purview of a backup admin. Even nevertheless the application is logging and tracking its activities, it truly is unusual for a backup admin to constantly observe that facts for anomalies. With this integration, Druva feeds that facts immediately to a security admin using FireEye Helix. Ananthakrishnan claimed Druva is discovering related degrees of integration with its other security partners.
Details defense seller Arcserve has similarly partnered with security seller Sophos to provide security for backups, though suppliers these as IBM and Acronis merge the two within their have offerings.






